Software developer and composer Stephen Coyle published a new article on his blog recently, intent on measuring the Bluetooth latency of Apple’s new AirPods Pro and comparing their performance to previous-generation AirPods. As Coyle pointed out, Bluetooth audio latency in wireless earphones can cheapen the user experience of these devices, […]
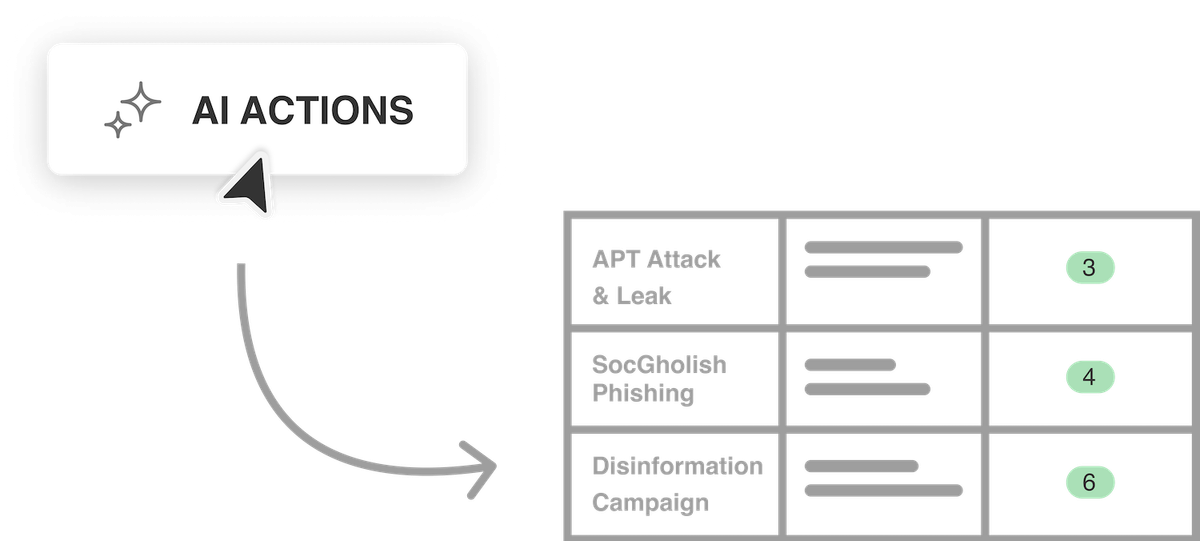
AI prompt guidance for generating a threat hunt hypothesis
Description This AI Actions prompt creates a threat hunt hypotheses in a tabular format that’s easy to read and integrate into reports or presentations. The hypotheses are derived from the selected articles, and procedures are extracted with sufficient detail to perform a real threat hunt. This enables hunters to plan […]
Linux Server Hardening Using Idempotency with Ansible: Part 3 | Linux.com
In the previous articles, we introduced idempotency as a way to approach your server’s security posture and looked at some specific Ansible examples, including the kernel, system accounts, and IPtables. In this final article of the series, we’ll look at a few more server-hardening examples and talk a little more […]